
Cryptography and network security
9 of 25 videos summarized
 6:53
6:53DES Weaknesses in Cryptography
Nov 27, 2019
 14:57
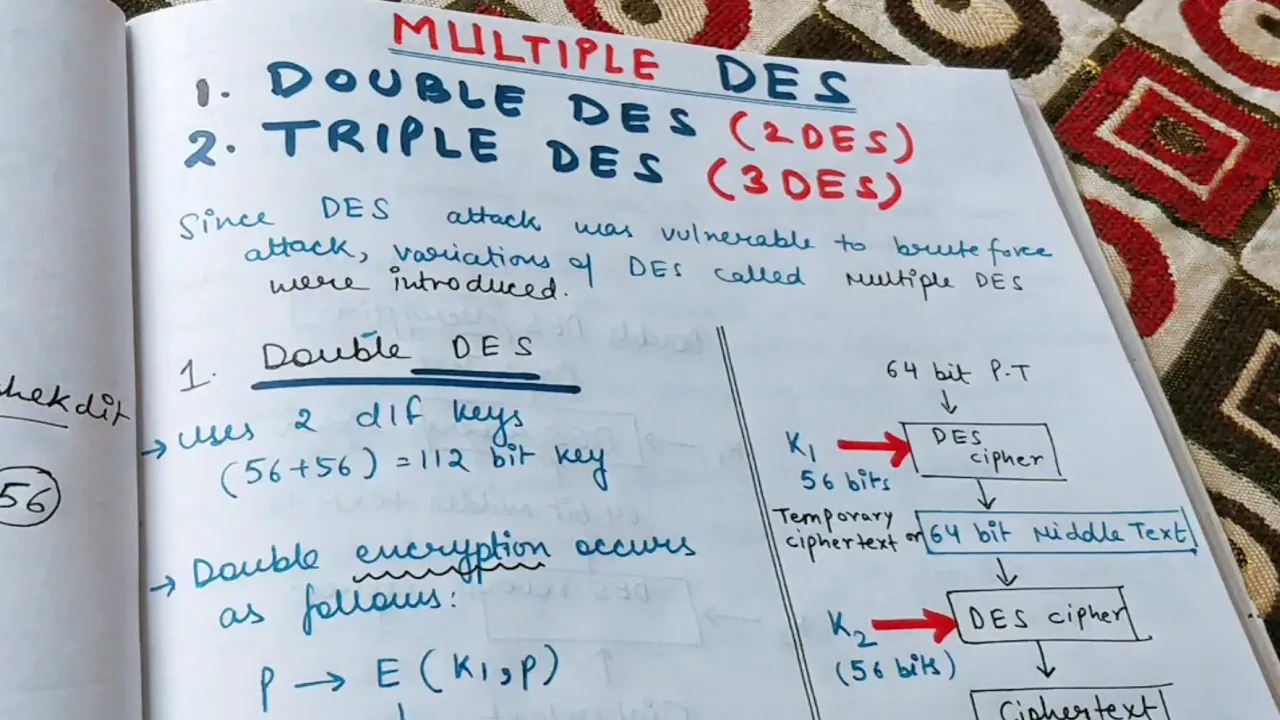
14:57Double DES and Meet in the middle attack in 2DES | DES part-3
Nov 24, 2019
 4:56
4:56Symmetric vs Asymmetric Cryptography | Cryptography and network security
Nov 12, 2019
 8:23
8:23Shannon's theory of Confusion and Diffusion | Cryptography and Network Security
Sep 19, 2019
 10:59
10:59Stream and Block Cipher | Difference between Stream and Block Cipher
Sep 19, 2019
 12:09
12:09Keyless and Keyed Transposition techniques | Types of transposition techniques in Cryptography
Sep 15, 2019
 6:33
6:33Security Mechanisms in Cryptography
Sep 9, 2019
 10:55
10:55Security Attacks in cryptography
Sep 9, 2019
 11:25
11:25Security Goals and Security Services | CIA Triad in Cryptography
Sep 8, 2019