Double DES and Meet in the middle attack in 2DES | DES part-3
स्वागत करता हूँ आपका अपने चैनल पर
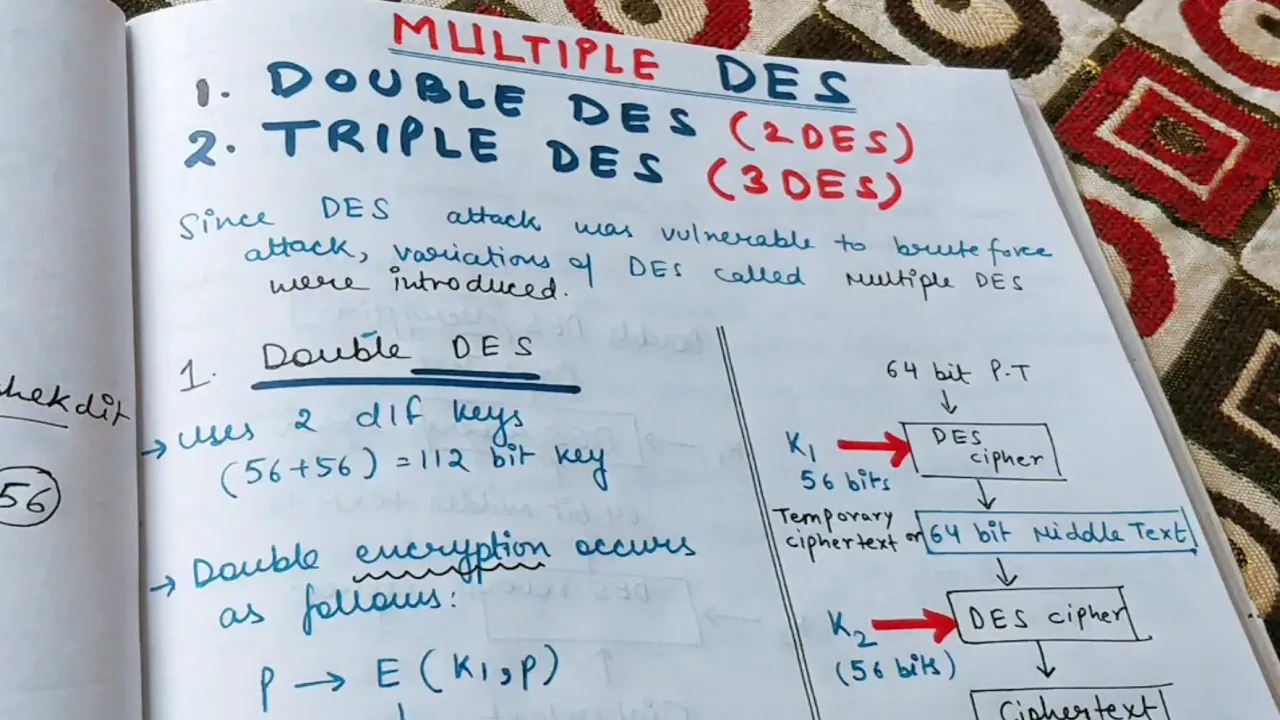
अनुभाग अवलोकन: इस वीडियो में हम मल्टी-पुल DES कॉन्सेप्ट के बारे में चर्चा करेंगे। DES के पहले 2 वीडियो में हमने DES को समझा है, 56 bit keys का प्रयोग किया है, परिक्रमाएं, encryption, decryption, brute force attack, multiple DES की introduction
Multi-Pull DES Concept
- पहले 2 videos में detailed details discuss किए गए
- Cryptographic series में multiple DES introduced
- Parallel computing techniques से multiple DES concept developed
- Multiple DES used to prevent brute force attacks on regular DES
- Double DES uses two different keys for encryption and decryption
- Encryption process explained using a block diagram
- Plain text passes through the entire double DES process to generate ciphertext
- Decryption process explained using a block diagram
- Ciphertext passes through the double DES process to generate plaintext
डेटा के साथ प्रदर्शन
अनुभाग अवलोकन: इस वीडियो में हम डेटा के साथ प्रदर्शन के बारे में चर्चा करेंगे।
Data Presentation
- 16 rounds of DES performed on the data
- Encryption and decryption processes explained with examples
- Use of different keys for encryption and decryption in multiple DES
डबल डाइस प्रक्रिया के बारे में
इस सेक्शन में हम डबल डाइस प्रक्रिया के बारे में चर्चा करेंगे। हम सिफरटेक्स्ट को प्लेनटेक्स्ट में कन्वर्ट करने की प्रक्रिया पर विचार करेंगे।
डबल डाइस प्रक्रिया
- 16 facial rounds होती हैं, dyes reverse cipher solid round होती है।
- Cipher text पर k2 use करना होता है, middle text मिलती है।
- Middle text पर double dyes process apply करनी होती है, k1 use करना होता है, plain text मिलती है।
- Cipher text पर k2 use करना होता है, plain text convert करनी होती है।
- Double dyes meet in the middle attack: pairs of cipher text and plain text are used for encryption and decryption, results are matched in the middle.
- Meet in the middle attack के लिए pairs of k2 use होते हैं, plain text को encrypt करना होता है और cipher text को decrypt करना होता है।
- Meet in the middle attack में plain text और cipher text के pairs की जानकारी चाहिए होती है, सभी combinations पर encryption apply की जाती है, 56 bit keys (K1 or K2) use होते हैं।
Meet in the Middle Attack
इस सेक्शन में meet in the middle attack पर विचार किया जाएगा, प्लेनटेक्स्ट और सिफरटेक्स्ट pairs का upyog encryption और decryption में किया जाता है।
Meet in the Middle Attack
- Meet in the middle attack requires knowledge of some plain text and its corresponding pair.
- Possible combinations of encryption with all 56-bit keys (K1 or K2) are performed on the plain text.
- The same is done for cipher text using decryption.
- Results obtained from both sides are sorted and compared to find a match.
MIM Attack: Explanation and Drawback
इस सेक्शन में meet in the middle attack के बारे में विस्तार से चर्चा की जाएगी, इसका drawback पर भी प्रकाश डाला जाएगा।
MIM Attack: Explanation and Drawback
- Meet in the middle attack involves encryption from one end and decryption from the other end, with results matched in the middle.
- The attack requires knowledge of some plain text and its corresponding pair.
- Encryption is performed on the plain text using all possible combinations of 56-bit keys (K1 or K2).
- Decryption is performed on the cipher text using all possible combinations of 56-bit keys (K1 or K2).
- Results obtained from both sides are compared to find a match.
- The drawback of meet in the middle attack is that it requires a large number of computations and storage for storing intermediate results.
MIM Attack: Implementation Steps
इस सेक्शन में meet in the middle attack के implementation steps पर प्रकाश डाला जाएगा।
MIM Attack: Implementation Steps
- Encrypt all possible combinations of plain text using 56-bit keys (K1 or K2).
- Store the encrypted results in a table.
- Decrypt all possible combinations of cipher text using 56-bit keys (K1 or K2).
- Compare the decrypted results with those stored in the table.
- Sort and analyze the obtained results to find matches.
MIM Attack: Limitations
इस सेक्शन में meet in the middle attack की limitations पर चर्चा की जाएगी।
MIM Attack: Limitations
- Meet in the middle attack requires knowledge of some plain text and its corresponding pair.
- The attack becomes more complex as the number of bits increases.
- It requires a large number of computations and storage for storing intermediate results.
- The success of the attack depends on the availability of pairs of plain text and cipher text.
Conclusion
इस सेक्शन में हमने meet in the middle attack के बारे में विस्तार से चर्चा की। हमने implementation steps, limitations, और drawbacks पर प्रकाश डाला।
Conclusion
- Meet in the middle attack is a technique that involves encryption from one end and decryption from the other end, with results matched in the middle.
- The attack requires knowledge of some plain text and its corresponding pair.
- It has limitations such as requiring a large number of computations and storage for storing intermediate results.
- Despite its drawbacks, meet in the middle attack can be effective when pairs of plain text and cipher text are available.