Digital Signature Algorithm (DSA) - Cryptography - Practical TLS
Digital Signature Algorithm Overview
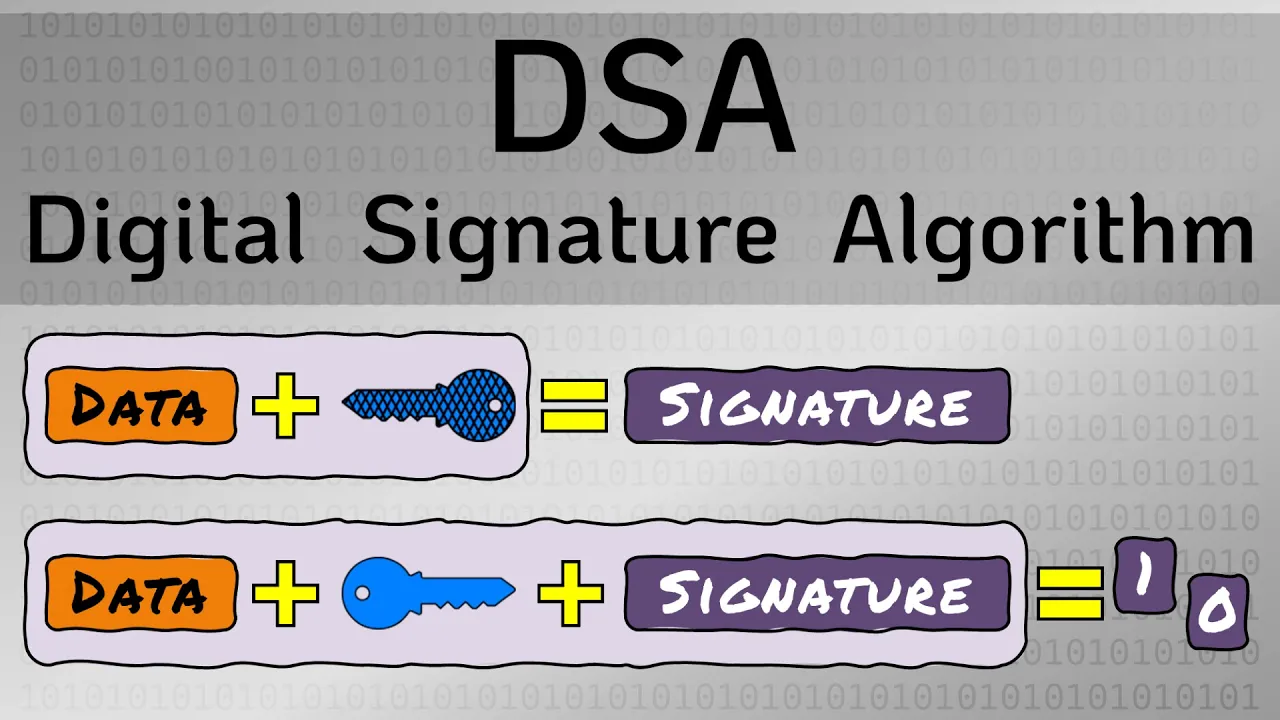
In this section, the Digital Signature Algorithm (DSA) is introduced and compared to other asymmetric encryption algorithms like RSA and Diffie-Hellman.
RSA Algorithm Functionality
- The RSA algorithm involves creating a pair of keys for encryption, decryption, and signatures.
DSA Specifics
- DSA can only be used for signature generation and verification.
Signature Generation Process
- DSA signature generation requires the message, private key, random number, and specific parameters.
Signature Verification Operation
- For signature verification in DSA, the message, public key corresponding to the private key used for signing, signature itself, and DSA parameters are needed.
Importance of Unique Random Numbers in DSA
This part emphasizes the critical role of unique random numbers in ensuring the security of the Digital Signature Algorithm.
Unique Random Number Importance
- Reusing random numbers in DSA can lead to catastrophic failures by exposing private keys.
Mitigating Duplicate Random Numbers
- Solutions include using sufficiently large random numbers or employing RFC 6979 for deterministic random number generation based on the message being signed.
Key Takeaways on Digital Signature Algorithm
Summarizing essential points about the Digital Signature Algorithm (DSA) and its distinct features compared to other asymmetric encryption protocols.
Main Points on DSA
- DSA is solely for signature generation and verification purposes.