Píldora formativa Thoth 44 ¿Cómo funciona el hash MD5?
MD5: Understanding the Algorithm and Its Vulnerabilities
Overview of MD5
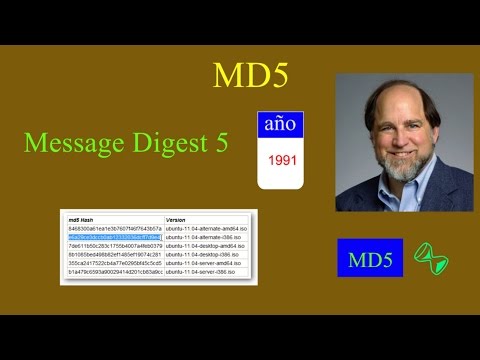
- MD5 stands for Message Digest number 5, an algorithm developed by Ron Rivest in 1991. It gained popularity due to its speed but has known design flaws since its inception.
- The MD5 hash produces a 128-bit summary (32 hexadecimal characters), regardless of the input file size.
Technical Details of MD5
- Input messages are divided into 512-bit blocks, with padding applied to complete the last block. Padding consists of a '1' followed by necessary zeros, reserving the last 64 bits for message length.
- Internally, MD5 processes words in little-endian format; thus, a word like "Amor" (hexadecimal: 41 6D 6F 72) is read as 72 6F 6D 41.
Processing Mechanism
- MD5 utilizes four public vectors (A, B, C, D), mixing them with the input's words through a series of operations over each block.
- After processing each block through multiple rounds (64 total per block), the final values of A, B, C, and D yield the overall hash.
Security Concerns
- Each input block undergoes transformations using four distinct functions across sixteen rounds. This complexity was initially thought to provide security against certain attacks.
- The theoretical strength against birthday paradox attacks is estimated at 2^64. However, practical vulnerabilities have reduced this to less than 2^24.
Real-world Implications