How SSL & TLS use Cryptographic tools to secure your data - Practical TLS
SSL and TLS Overview
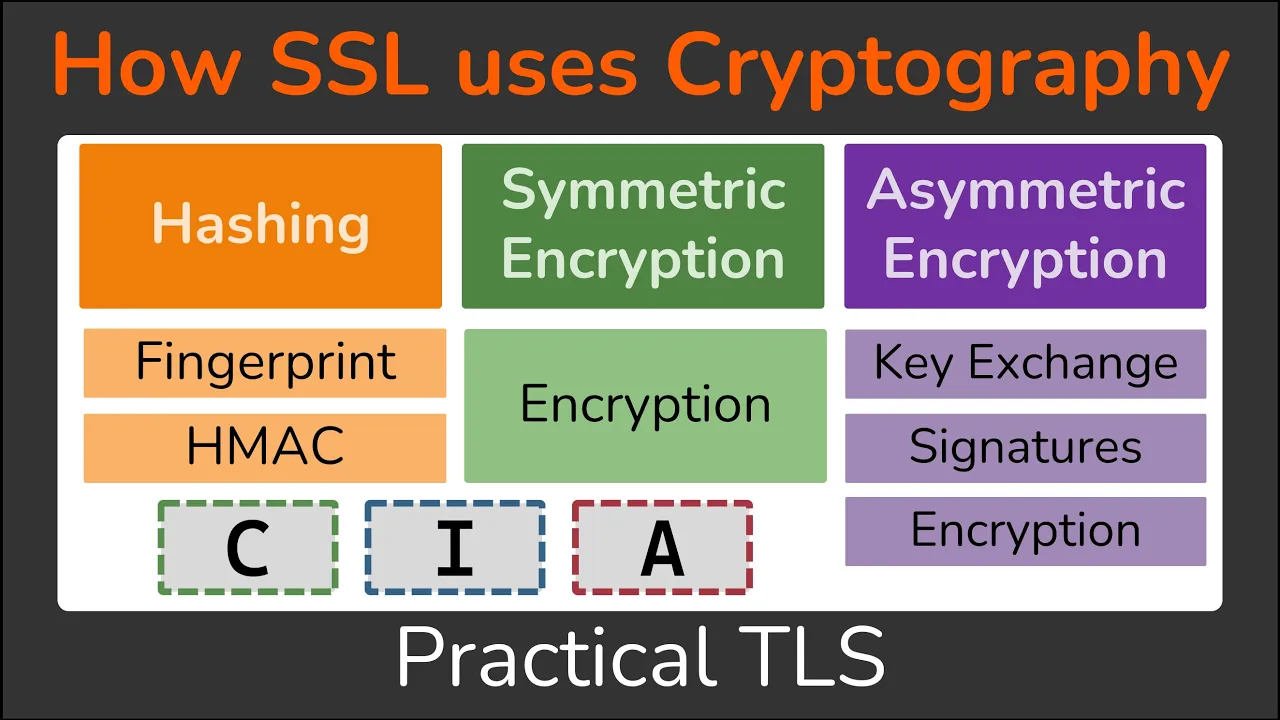
In this section, the instructor provides an overview of how SSL and TLS utilize cryptographic tools for data security.
Understanding the Main Purposes of SSL and TLS
- Confidentiality ensures data is only accessible by the client and server. Integrity guarantees data cannot be modified between them. Authentication confirms the identity of communication partners.
- Cryptographic tools like encryption, hashing, and PKI are used to provide these services. Encryption offers confidentiality, hashing ensures integrity, and PKI facilitates authentication.
Exploring Cryptographic Tools
- Hashing creates a message fingerprint for integrity. MACs combine messages with secret keys for integrity and authentication. Symmetric encryption is solely for confidentiality purposes.
- Asymmetric encryption enables key exchange for shared keys, ensuring confidentiality, integrity, and authentication through symmetric encryption and MACs. Signatures can also provide integrity and authentication.
Application in SSL/TLS
- SSL/TLS use cryptographic tools to secure data between clients (web browsers) and servers (websites). They employ symmetric encryption for confidentiality and MACs for integrity on bulk data exchanges.
- Establishing mutual secret keys via asymmetric encryption precedes applying symmetric keys for confidentiality/integrity but lacks authentication assurance until certificate authorities issue certificates linking identities to public keys.
Role of Certificate Authorities
- Certificate authorities generate certificates linking keys to identities for authentication assurance in asymmetric key exchanges. Clients trust certificate authorities' signatures on certificates as proof of authenticity, ensuring secure communication channels with authenticated symmetric keys derived from these exchanges.
Public Key Infrastructure (PKI) Overview
In this section, the concept of Public Key Infrastructure (PKI) is introduced, emphasizing its role in SSL/TLS protocols for securing communication.
Understanding PKI and Cryptographic Tools
- The video discusses the significance of PKI (Public Key Infrastructure) within SSL/TLS protocols.
- Emphasizes the utilization of cryptographic tools to establish symmetric keys for ensuring confidentiality and integrity in communication.
Conclusion and Course Promotion
The conclusion of the lesson is summarized, inviting viewers to explore a comprehensive course on SSL/TLS for further learning.
Wrapping Up the Lesson
- Viewers are encouraged to proceed to the next lesson if they have grasped symmetric key generation using cryptographic tools.
- The video expresses gratitude to viewers and hints at upcoming lessons in the course.
Course Promotion: Practical TLS
A promotion for a detailed course on SSL/TLS, highlighting its content and benefits for those interested in becoming proficient in SSL expertise.
Details about Practical TLS Course
- Introduction to "Practical TLS," a comprehensive course diving deep into SSL/TLS concepts methodically with easy-to-understand illustrations.
- Covers topics such as cryptography, certificates, private keys, handshake processes, OpenSSL usage, and more.