Diffie-Hellman Key Exchange - the MAGIC that makes it possible - Cryptography - Practical TLS
Diffie-Hellman Protocol Overview
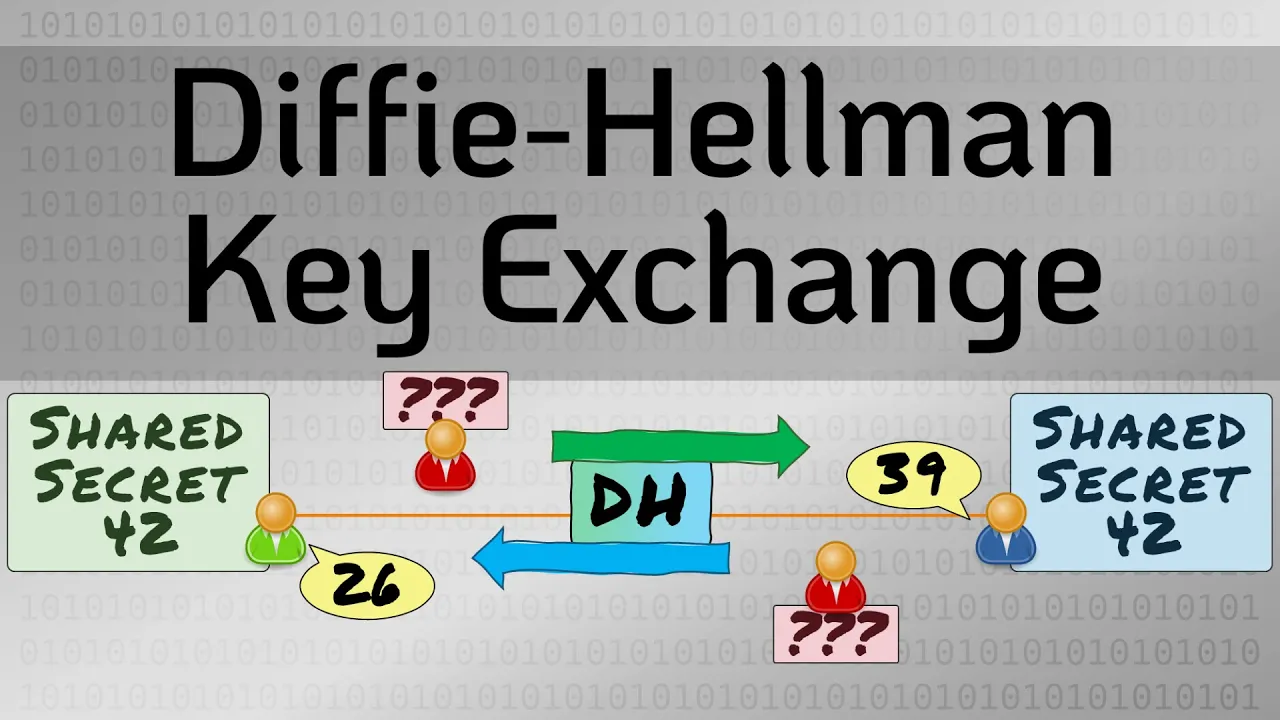
The Diffie-Hellman protocol is an asymmetric encryption algorithm that enables two parties to establish a shared secret over an unsecured medium by exchanging values without directly transmitting the shared secret.
Establishing Shared Secret
- Diffie-Hellman allows users to exchange public values and combine them with private values to derive a shared secret, ensuring confidentiality even if public values are intercepted.
- Alice and Bob agree on prime number (13) and generator (6), generate private keys (5 and 4), calculate public keys, exchange them, and compute the shared secret using exchanged public values and private keys.
Shared Secret Calculation
- Alice computes her public value as 2, Bob's as 9; they exchange these values. Then, Alice calculates the shared secret as 3 by combining Bob's public value with her private key.
- Both parties arrive at the same shared secret of 3 through their calculations. Eavesdroppers only hear exchanged numbers but cannot deduce the shared secret due to Diffie-Hellman's security properties.
Security of Diffie-Hellman
The security of Diffie-Hellman lies in the discrete logarithm problem, which makes it computationally infeasible for attackers to determine the shared secret through brute force.
Discrete Logarithm Problem
- Security of Diffie-Hellman relies on the discrete logarithm problem where solving for x in g^x ≡ n (mod p) is challenging due to modulo operations.
- Discrete logarithm problems like g^x ≡ n (mod p) have no efficient solution other than brute force, making it time-consuming for attackers to break Diffie-Hellman encryption.
Key Takeaways
Understanding the purpose of Diffie-Hellman in establishing secure communication over untrusted channels is crucial. Its security stems from leveraging large numbers that resist brute-force attacks effectively.
Main Points
- Key takeaway: Diffie-Hellman enables secure establishment of a shared secret between two parties over insecure networks by leveraging complex mathematical problems that ensure confidentiality.