Redes: Topología Física vs. Lógica Explicada
Understanding Network Topologies
In this section, the video introduces the importance of understanding physical and logical network topologies for individuals interested in computer networks. It explains various network architectures to help organizations choose the most suitable one for their needs.
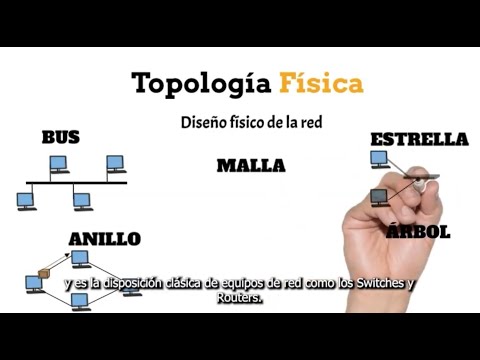
Defining Physical Topologies
- The video starts by defining physical topologies and discussing common ones, highlighting the advantages and disadvantages of each.
- Physical topologies refer to the physical design of a network, considering how individual components are interconnected. They include bus, star, ring, mesh, and tree topologies.
Exploring Bus and Ring Topologies
- In a bus topology, all components are connected on a single line with drawbacks like single point failure affecting all nodes' communication.
- A ring topology involves components forming a loop where a token circulates for controlled transmission. Only one device can transmit at a time.
Understanding Star Topology
- Star topology is widely used with all devices connected to a central hub providing efficient data transmission without collisions.
- When using a switch as the central device in star topology, it allows simultaneous information transmission from all nodes ensuring privacy for data delivery.
Diving into Mesh and Tree Topologies
- Mesh topology offers multiple paths for signal travel with complete or partial connections among stations.
- Tree topology organizes components hierarchically facilitating data flow up and down the hierarchy based on specific requirements and network environment.
Logical Network Structures
This part delves into logical network structures focusing on how data is sent between nodes independently of physical design. It covers examples like Point-to-Point, Broadcast, and Hierarchical topologies.
Exploring Logical Network Designs
- Logical network structures consider protocols for data transmission control access error recovery. Examples include Point-to-Point direct transmissions between two nodes.
- Two methods of medium access control are discussed: best effort where devices listen before transmitting to avoid collisions; controlled access where devices wait for their turn to transmit using protocols like CSMA/CD.
Conclusion