Data Integrity - How Hashing is used to ensure data isn't modified - HMAC - Cryptography
Data Integrity and Hashing Algorithms
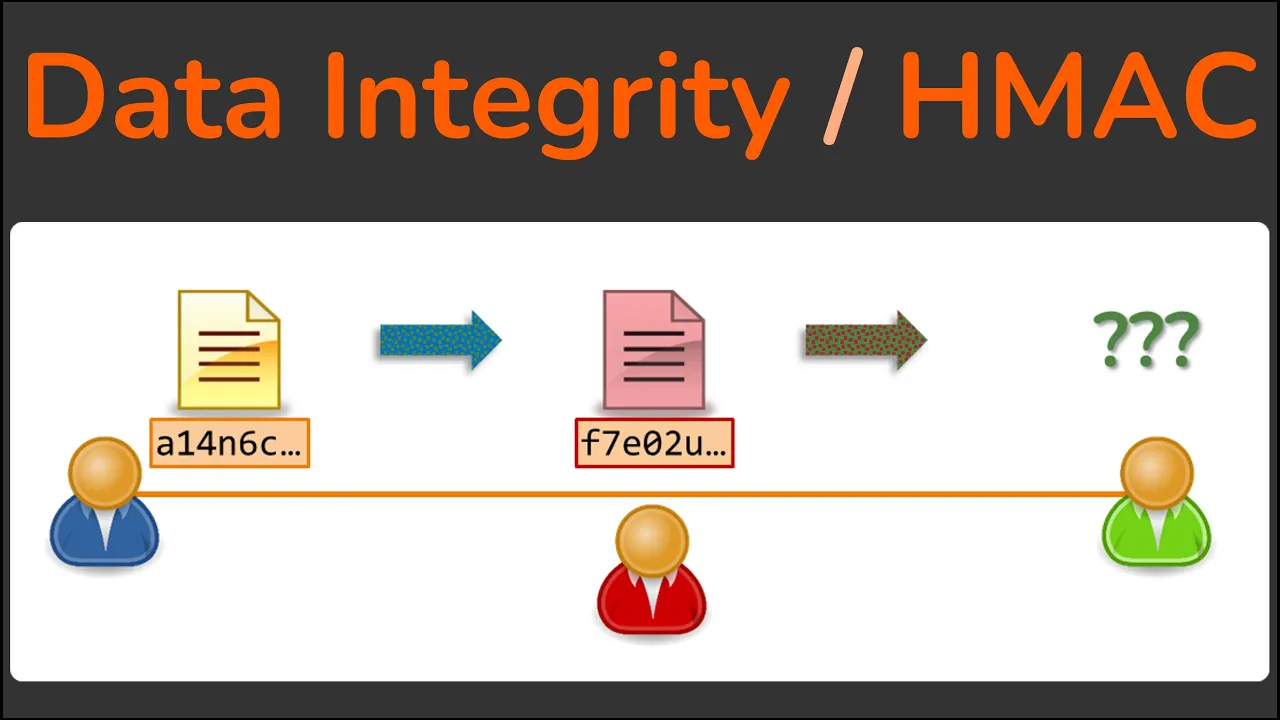
In this section, the concept of data integrity and how hashing algorithms contribute to ensuring data integrity are discussed.
Understanding Data Integrity and Hashing
- Hashing algorithms like MD5 or SHA-1 are used to calculate digests from messages for data integrity.
- Sending both the message and its digest ensures that the message was not altered in transit.
- The vulnerability of this method lies in potential interception and modification of the message by an attacker.
- Establishing a mutual secret key between sender and receiver is crucial for enhancing data integrity.
Message Authentication Code (MAC) for Data Integrity
- Mutual secret keys are combined with messages to calculate digests, ensuring message authenticity.
- MAC proves that messages were not tampered with during transmission and authenticates the sender's identity.
- HMAC (Hash-based Message Authentication Code) specifies how keys are combined with messages for integrity verification.
Key Takeaways
- Hashing algorithms produce message digests, while MAC involves combining messages with secret keys for authentication.
Lesson Conclusion
The instructor invites learners to explore more about SSL and TLS by enrolling in a comprehensive course called "Practical TLS," promising to transform participants into SSL experts.
Practical TLS Course Advertisement
- Enroll in the "Practical TLS" course for an in-depth understanding of the SSL and TLS ecosystem.
- The course aims to make participants SSL experts, regardless of their current knowledge level.
- Explore the world of SSL and TLS through this comprehensive deep dive.
- Gain the necessary expertise to navigate the complexities of SSL and TLS effectively.