What is Identification, Authentication, Authorization, Auditing, Accountability| IAAA| Cybersecurity
Understanding IAAA in Cybersecurity
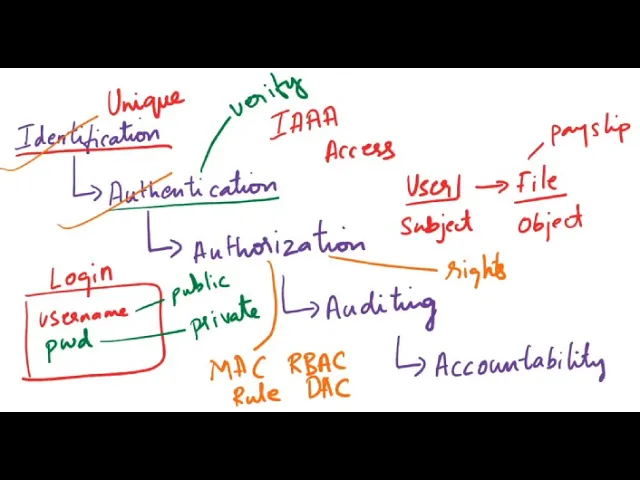
Introduction to IAAA Concepts
- The session introduces the concepts of Identification, Authentication, Authorization, Auditing, and Accountability (IAAA) in cybersecurity.
- These concepts are essential for access control and security management.
Identification
- Identification is the process of recognizing a user or subject. For example, providing a username or email ID during login.
- Unique identities are typically assigned to users; however, admin accounts may share common identifiers like "admin."
- Public information often constitutes identification data (e.g., names and email addresses).
Authentication
- Authentication verifies the claimed identity through methods such as passwords or PINs.
- There are four types of authentication:
- Type 1: Something you know (password/PIN).
- Type 2: Something you have (access card/token).
- Type 3: Biometrics (fingerprints/retina scans).
- Type 4: Somewhere you are (location-based access).
Single-Factor vs Multi-Factor Authentication
- Single-Factor Authentication (SFA): Requires one type of verification method.
- Multi-Factor Authentication (MFA): Involves two or more different types of authentication methods for enhanced security.
Authorization
- After successful authentication, authorization determines what actions a user can perform on resources.
- Example: A user should only access their payslip and not others' due to authorization constraints.
- Authorization is governed by various models such as Mandatory Access Control (MAC), Role-Based Access Control (RBAC), and Discretionary Access Control (DAC).
Auditing
- Auditing involves monitoring actions taken by users to ensure compliance with security policies.
- It records events related to logins and system activities for accountability purposes.
Accountability
- Accountability ensures that users are held responsible for their actions within systems.
Understanding Accountability in Information Security
Definition and Importance of Accountability
- Accountability is defined as the principle where an individual is responsible for safeguarding and controlling equipment, keying material, and information. They are answerable to proper authority for any loss or misuse of that information.
- Authentic accountability ensures that every information asset is owned by a subject (user), making them responsible for actions taken on that asset, which can include databases, files, applications, or systems.
Ownership and Security Policies
- Ownership of information assets is crucial for enforcing organizational security policies. Effective accountability requires proving a subject's identity and tracking their activities.
- Accountability involves reviewing log files collected during audits to check for compliance violations. This process helps ensure subjects are performing their duties correctly without unauthorized actions.
Identification and Non-repudiation
- The identification step initiates accountability processes. Achieving non-repudiation—where users cannot deny their actions—is facilitated through identification, authentication, authorization, auditing, and accountability.