Public Key Infrastructure - What is a PKI? - Cryptography - Practical TLS
New Section
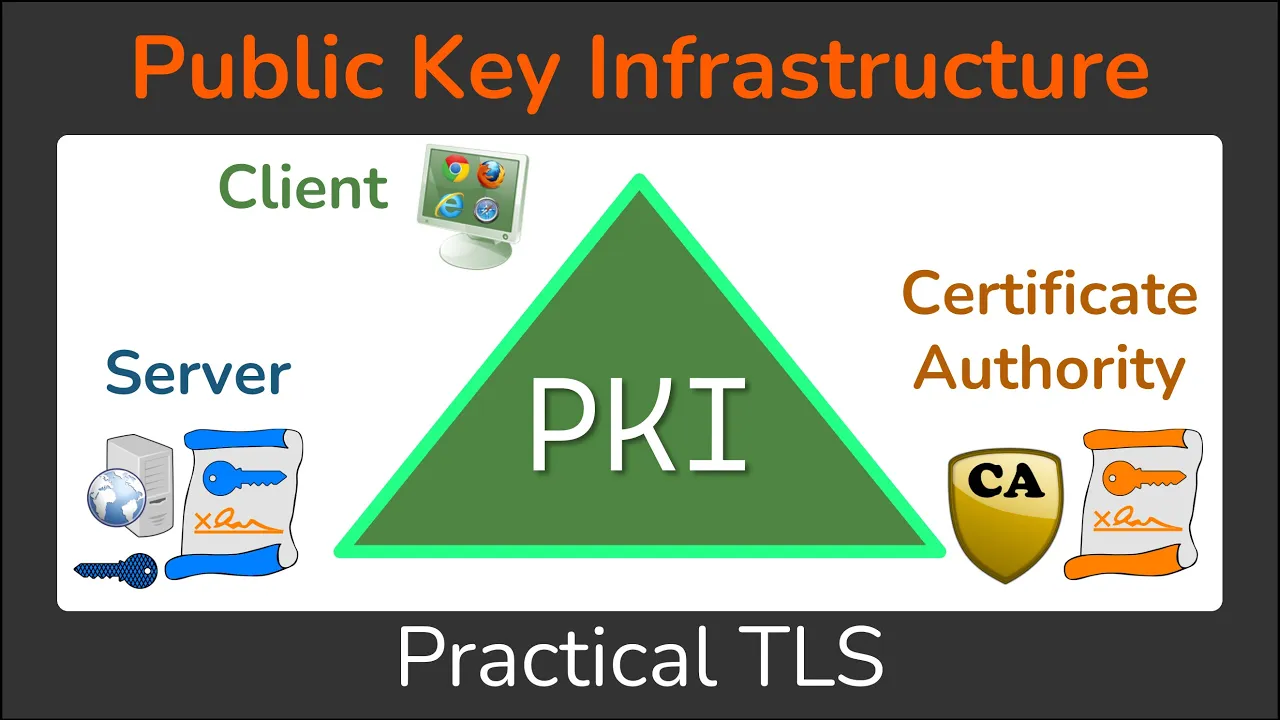
In this section, the importance of Public Key Infrastructure (PKI) in ensuring confidentiality, integrity, and authentication in communication systems is discussed.
The Role of Entities in PKI
- PKI involves three key entities: client, server, and certificate authority (CA).
- The client needs secure connections or identity verification, the server proves its identity, and the CA verifies identities and generates certificates.
- In the web PKI scenario, clients are browsers like Chrome or Firefox, servers are websites like Google.com, and CAs are public web certificate authorities.
Different Types of PKIs
- Apart from web PKIs, there exist other types like code signing PKIs for software verification.
- Code signing PKIs involve entities such as operating systems as clients verifying software identities with specific CAs.
Corporate Internal PKIs
- Many corporations have internal corporate PKIs for securing internal resources without relying on public CAs.
- Corporations establish their own internal CAs to sign certificates for internal resources accessed by employees.
Understanding a PKI
This section emphasizes comprehending the components that constitute a Public Key Infrastructure (PKI).
Importance of a PKI
- A PKI comprises clients, servers, and CAs essential for establishing secure communication channels.