Hashing, Hashing Algorithms, and Collisions - Cryptography - Practical TLS
Hashing Algorithms Explained
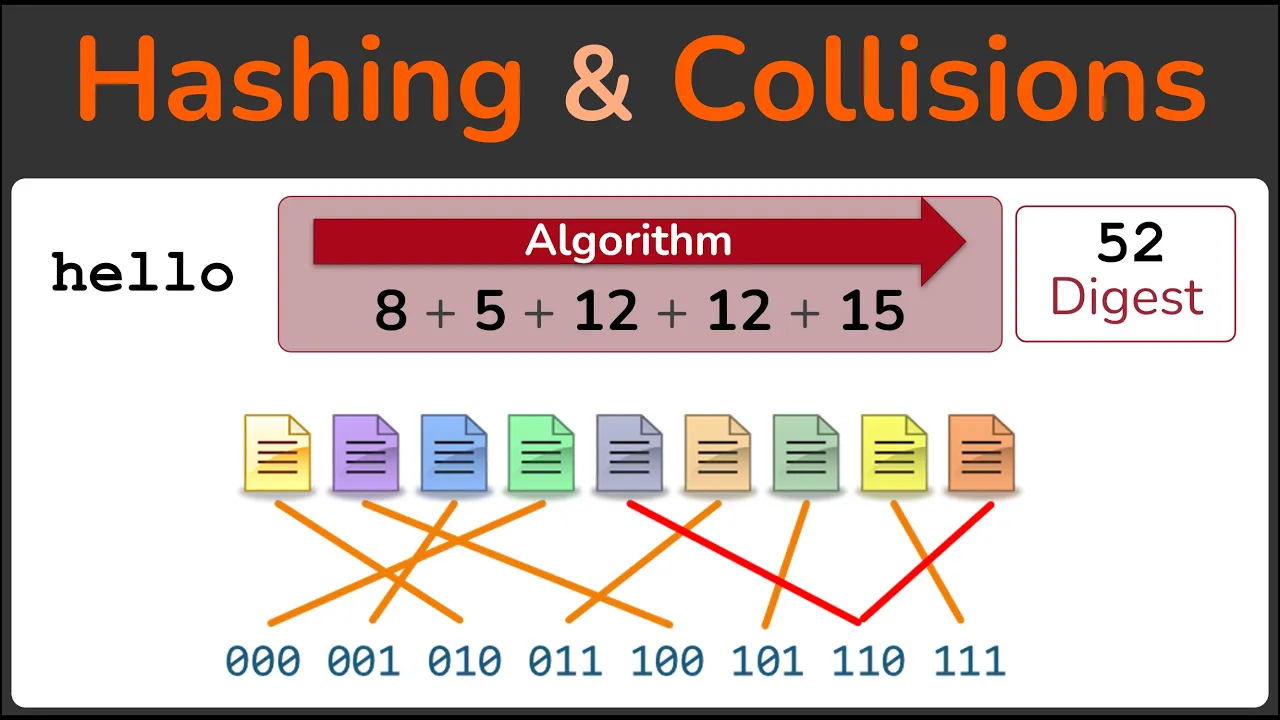
In this section, the concept of hashing algorithms is introduced, explaining how they generate a unique fingerprint or message digest for input messages.
Introduction to Hashing Algorithms
- A hashing algorithm processes input messages to produce a unique fingerprint or message digest.
- The output of a hashing algorithm is known as a message digest and can be referred to by various names like checksum, hash, or CRC.
- Message digests allow comparison between original messages to determine if they are the same or different.
Requirements for Hashing Algorithms
- Real-world hashing algorithms must make it infeasible to produce a given digest easily.
- It should be impossible to extract the original message from the digest (one-way encryption).
- Small changes in the original message should result in significant differences in the resulting digest.
- The resulting digest length should always be fixed regardless of the input size.
Demonstrating Hashing with MD5 Algorithm
- Using the MD5 algorithm as an example of a real-world hashing algorithm that meets all requirements.
- Demonstrating how to calculate the MD5 hash of a message using Linux utilities like echo and md5sum.
Hashing Algorithms and Collisions
In this section, the instructor explains hashing algorithms, their properties, and the concept of collisions in detail.
Understanding Hashing Algorithms
- Hashing involves creating a hash from a given string using an algorithm.
- The resulting digest remains the same regardless of whether the input is a single letter or a sentence.
- Hashing algorithms iterate over the message multiple times to produce a fixed-width digest, showcasing the avalanche effect.
Collisions in Hashing
- A collision occurs when two different messages result in the same digest, which defeats the purpose of hashing for comparison.
- Collisions are inevitable due to limited possible digests in hashing algorithms.
Types of Hashing Algorithms
This part introduces various hashing algorithms commonly used and discusses their characteristics.
Commonly Used Hashing Algorithms
- MD5 and SHA-1 are popular hashing algorithms producing 128-bit or 160-bit digests.
- The SHA-2 family offers different digest lengths based on security needs.