Network Scanning - TCP Flags & TCP 3-Way Handshake
Introduction to Active Information Gathering and Scanning
Overview of Scanning
- The video introduces the topic of scanning as part of a penetration testing boot camp, transitioning from passive information gathering to active methods.
- Scanning is defined as a process that follows extensive passive reconnaissance, focusing on identifying active targets and potential access vectors like ports and services.
- The goal of scanning is to create a profile of the target, including details such as operating system versions and service configurations.
Objectives of Scanning
- Key objectives include host discovery, operating system detection, and service identification. This helps prioritize vulnerabilities effectively.
- The importance of understanding low-hanging fruit in security assessments is emphasized; knowing what services are running aids in targeting weaknesses first.
Types of Scanning
Network vs. Port Scanning
- Network scanning aims to identify active hosts within a network to map out its infrastructure, including connections between resources like file servers or mail servers.
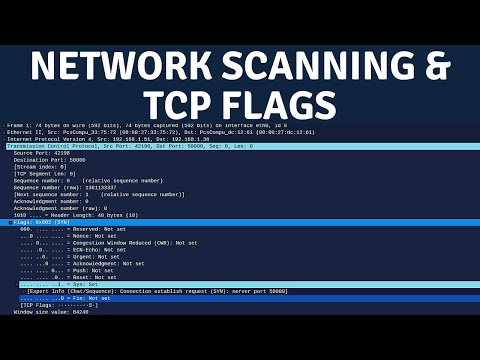
- Port scanning involves probing specific TCP flags to enumerate running services on identified hosts based on their responses.
TCP Flags in Port Scanning
- TCP flags play a crucial role in how data packets are transmitted across networks; they help determine the target's operating system and check for firewalls or packet filtering.
Understanding TCP Flags
Key TCP Flags Explained
- The urgent flag indicates that a packet should be processed immediately by the receiving device.
- The push (PSH) flag prompts immediate data transmission; the FIN flag signals the end of transmission while ACK acknowledges receipt of packets.
Importance of Three-Way Handshake
Connection Initialization
Understanding TCP and UDP Communication
TCP vs. UDP Communication
- TCP (Transmission Control Protocol) is a connection-based communication method, requiring an established connection before sending packets.
- In contrast, UDP (User Datagram Protocol) is connectionless, allowing packets to be sent without prior establishment of a connection.
The Three-Way Handshake in TCP
- The three-way handshake involves the client sending a SYN packet to the server to initiate a connection.
- Upon receiving the SYN packet, the server changes its state to "SYN received" and responds with a SYN-ACK packet.
- The client then sends an ACK (acknowledgment) packet back to the server, completing the handshake and establishing communication.
Scanning Techniques Using TCP
- A full scan establishes a TCP three-way handshake with all specified ports on the target; responses indicate whether services are running or if ports are active.
- If no response is received from a port, it is likely inactive; if there is a response, that port may be open.
Stealth Scanning Methodology
- In stealth scanning, only SYN packets are sent followed by an acknowledgment; instead of completing connections, they are reset using the RST flag to avoid detection.
Upcoming Topics in Nmap Usage
- Future discussions will cover host discovery, OS and service detection, UDP scanning techniques, stealth scans, firewall evasion strategies, and an introduction to the Nmap scripting engine.